Site Search:
Top CompTIA Exams
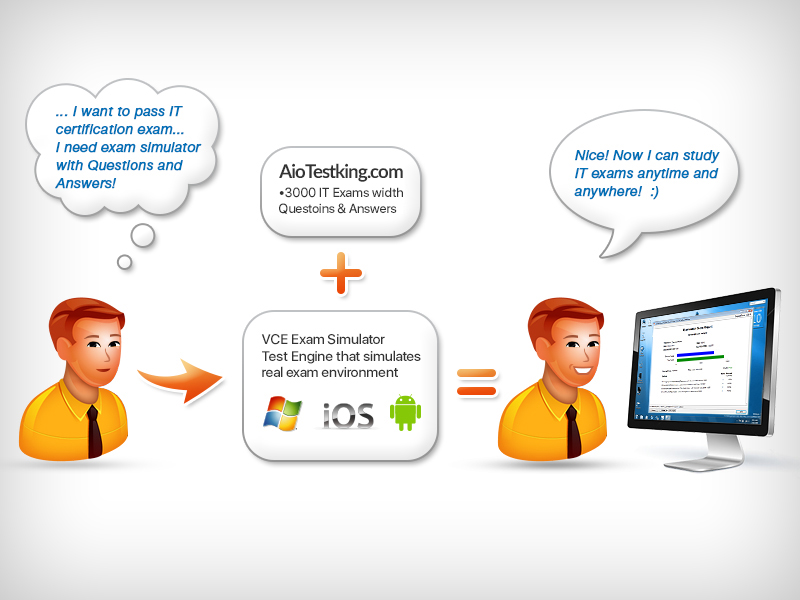
100% Real Free CompTIA Certification Practice Test Dumps & Training Course to Study and Prepare for Real CompTIA Exam Fast. All CompTIA Certification Exams are covered by our detailed collection of VCE Exam Dumps & Certification Training Courses. CompTIA Certifications are acquired by studying the Practice Exam Questions and taking the exam using the Avanset VCE Exam Simulator. Pass your CompTIA Certification Exams using Dumps with confidence!
| Exam | Title | Files |
|---|---|---|
| 220-1001 | CompTIA A+ Certification Exam: Core 1 | 10 |
| 220-1002 | CompTIA A+ Certification Exam: Core 2 | 5 |
| 220-1101 | CompTIA A+ Certification Exam: Core 1 | 1 |
| 220-1102 | CompTIA A+ Certification Exam: Core 2 | 1 |
| CAS-004 | CompTIA Advanced Security Practitioner (CASP+) CAS-004 | 5 |
| CLO-002 | CompTIA Cloud Essentials+ | 2 |
| CS0-003 | CompTIA CySA+ (CS0-003) | 1 |
| CV0-003 | CompTIA Cloud+ | 5 |
| DA0-001 | Data+ | 1 |
| DS0-001 | CompTIA DataSys+ | 1 |
| FC0-U51 | CompTIA IT Fundamentals | 2 |
| FC0-U61 | CompTIA IT Fundamentals | 5 |
| N10-008 | CompTIA Network+ | 4 |
| PK0-005 | CompTIA Project+ | 2 |
| PT0-002 | CompTIA PenTest+ Certification Exam | 1 |
| SK0-005 | CompTIA Server+ Certification Exam | 3 |
| SY0-601 | CompTIA Security+ | 4 |
| SY0-701 | CompTIA Security+ 2023 | 1 |
| TK0-201 | CompTIA CTT+ Essentials | 2 |
| XK0-005 | CompTIA Linux+ | 2 |
CompTIA Certifications
leah
- Brazil
- Sep 16, 2020
wow! i have used cas-002 vce files and passed my comptia exam. i am grateful guys.
isabel
- Peru
- Sep 15, 2020
i have passed my cs0-001 exam easily. the secret to excelling in this exam is utilizing practice cs0-001 questions and answers. i believe every candidate who uses them in the prep always excel.
fiona
- Bangladesh
- Sep 13, 2020
@rose,you are sailing on the right track… go ahead and use it in your revision. i passed my test last week using premium files for fc0-u51. use it and you will score an excellent grade.
rose
- South Korea
- Sep 09, 2020
who has used fc0-u51 premium file to tell whether its reliable? i will be taking fc0-u51 cert exam next month and I want to use it in my revision.
catherine
- Mexico
- Sep 07, 2020
@nico, you just need to read a wide variety of exam material for 220-901 cert exam. there are many learning resources with information relevant to this exam on this website and i am confident they will help perform incredibly.
flora
- Singapore
- Sep 07, 2020
hello guys, please share any clo-001 prep material you feel is important for those of us who are preparing for comptia cert exams. whoever has any material that can help me perform well in exam kindly share.
clifford
- United Kingdom
- Sep 05, 2020
i used comptia dumps for fc0-u51 in the exam preparation. i can’t believe i have scored the best grade ever.
crispin
- Ghana
- Sep 04, 2020
i have discovered that comptia training course for cv0-001 cert exam contains more than 70 percent of the actual concepts examined in the test. if you take it seriously for sure you will pass the exam. after going through it, i performed very well in the exam.
jemma
- United Kingdom
- Aug 31, 2020
the best way to revise for exam of comptia 220-902 is by the use of comptia practice test. it comprises questions which help to determine you weak points as far as the exam is concerned. after determining the weak points you will be able study further so as to avoid failure.
nico
- Myanmar
- Aug 29, 2020
i need someone who has passed comptia exam to guide me a little. i am waiting for 220-902 exam and I don’t know how to go about it.
cyprian
- Thailand
- Aug 26, 2020
you don’t have to be worried on how to pass any of comptia certification exams. the information you need to know in order to pass them is contained in the comptia vce files. i used them in my preparation for 220-901 exam and they helped me so much.
What is CompTIA IT Certification?
CompTIA IT certification helps professionals by boosting their careers in the field of IT. These individuals have a better hold on the understanding of the various areas of IT. CompTIA’s vendor neutral program for certification is one of the most established within the IT industry. This helps in broadening their knowledge sphere and establishing themselves as experts in the IT framework. It is an entry-level certification which is specifically designed to help users to learn the basic principles of computers. The certification covers the vast range of concepts in IT along with its wide terminology.Benefits of the Certification
Individuals who are looking for a starting point in computers prefer this certification as it covers the basic fundamental concepts. The certification can be significant for those who are looking for a career change and begin as a developer in the IT sector. This is the initial certification that individuals pursue. The concepts covered over this certification are mostly the basics of hardware along with troubleshooting of the system. This also includes the installation of software and security along with networking. Your ability will be recognized at an international level. This exam can be a stepping stone in your career.The exams in this certification are as follows:
Exam FC0-U51: The exam covers the basics of IT concepts which comprises of identification and explanation of different components of a computer. It also includes concepts on the installation and establishment of various network connections along with taking measures to prevent security risks.The exam consists of 75 questions, which are of multiple-choice type. The total duration is 60 minutes, and it is available in more than 8 languages. There are no prerequisites for appearing in this exam. The passing score for this exam is 650 out of 900 possible points.
Exam FC0-U61 is a new version issued in 2018. The exam deals with the different skills and concepts required to explain the basics of IT. It includes computing as well as the development of the software with the utilization of the database.
The passing score for this exam stands at 650 out of the total points of 900. The total number of the questions included in the exam is 100. There is no prerequisite for appearing in this certification exam. The exam is available only in the English language.
Exam Focus:
Both exams focus on the essential IT skills and concepts which are required to perform various tasks. Individuals with this certification will be able to use the features and functions of the operating systems. Along with that, they will be able to establish network connectivity and identify various software applications and their uses. They will be able to use the security and web browsing methods efficiently.How to Open VCE Files
Use VCE Exam Simulator to open VCE files.
| VCE Exam Simulator For Windows |
|
| VCE Simulator For Mobile For Android |
|
| VCE Simulator For Mobile For iPhone |
|
| VCE Simulator For Mac OS X |